Zero Trust: A Security Concept for the Digital World
Why We Need to Rethink Cyber Security as We Know ItThe digital world is changing faster than ever. We are constantly connected online and the number of electronic devices and…
Why We Need to Rethink Cyber Security as We Know ItThe digital world is changing faster than ever. We are constantly connected online and the number of electronic devices and…
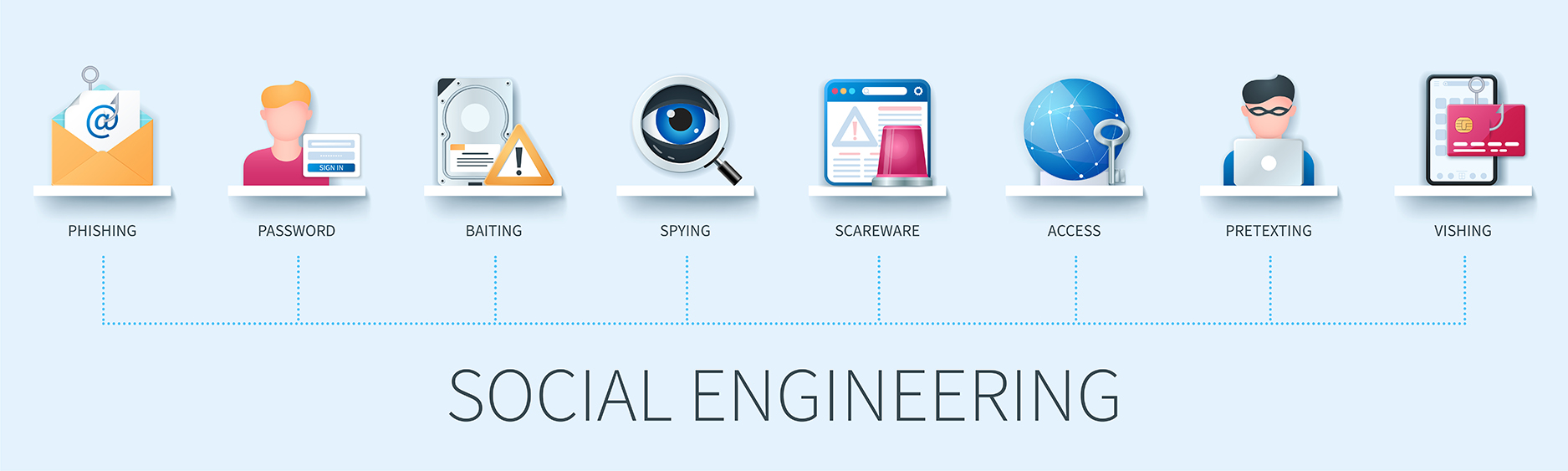
What are Social Engineering Attacks?Social Engineering is an act of manipulating people to expose confidential or sensitive information.This can be done by telephone, email, or face-to-face contact. It is the…
DETECT THREATS FASTER to avoid being the next breach headline. Join our Live Webinar with experts from NETWRIX and Multipoint Group and learn how to: Detect threats faster to avoid…
In recent weeks the Ukrainian Army and some major banks were subject to DDoS attacks. These attacks aim to severely impair and disrupt critical business services and they can happen…
According to the Vanson Bourne report, 31% of IT decision makers globally noted that their organization requires data to be encrypted whether it's at rest or in transit and 24%…
Qualys, Inc., a pioneer and leading provider of cloud-based security and compliance solutions, today announced its new Vulnerability Management, Detection and Response (VMDR) app to provide customers with one streamlined…
An integral part of every business is business processes that run as smoothly as possible – and one application that promises to automate and facilitate these processes is Enterprise Resource…
Malwarebytes products have a proven record of protecting computers by completely removing all forms of malware including viruses, trojans, spyware, adware, and rootkits. Intelligent heuristics and behavior based malware detection…
Corporations remain under significant pressure to conduct internal investigations for a variety of serious matters, such as alleged employee misconduct, whistleblower reports and data breach incidents. NAVEX Global’s 2018 Incident Management…