Tenable
Exposure Management for the Modern Attack Surface
A Word from the CyberLion
Main Features
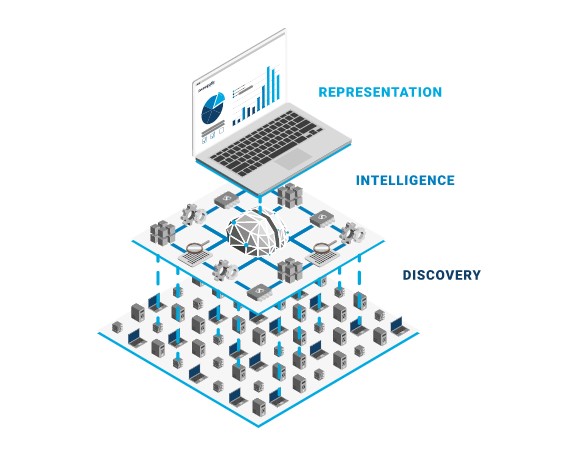
Discover Everything
Continuously identify assets and exposures across IT, cloud, containers, OT, web apps and identity systems.
Prioritize What Matters
Leverage contextual risk scoring and threat intelligence to focus on vulnerabilities most likely to be exploited.
Take Action
Deliver clear remediation guidance aligned with business risk
A new standard for securing AI
With the world’s leading AI-powered exposure management platform
Tenable is a Leader in the 2025 Gartner® Magic Quadrant™
Tenable is positioned furthest to the right for Completeness of Vision and highest for Ability to Execute among the 20 vendors included in the report.
Product Suite
Tenable One
Unified exposure management platform
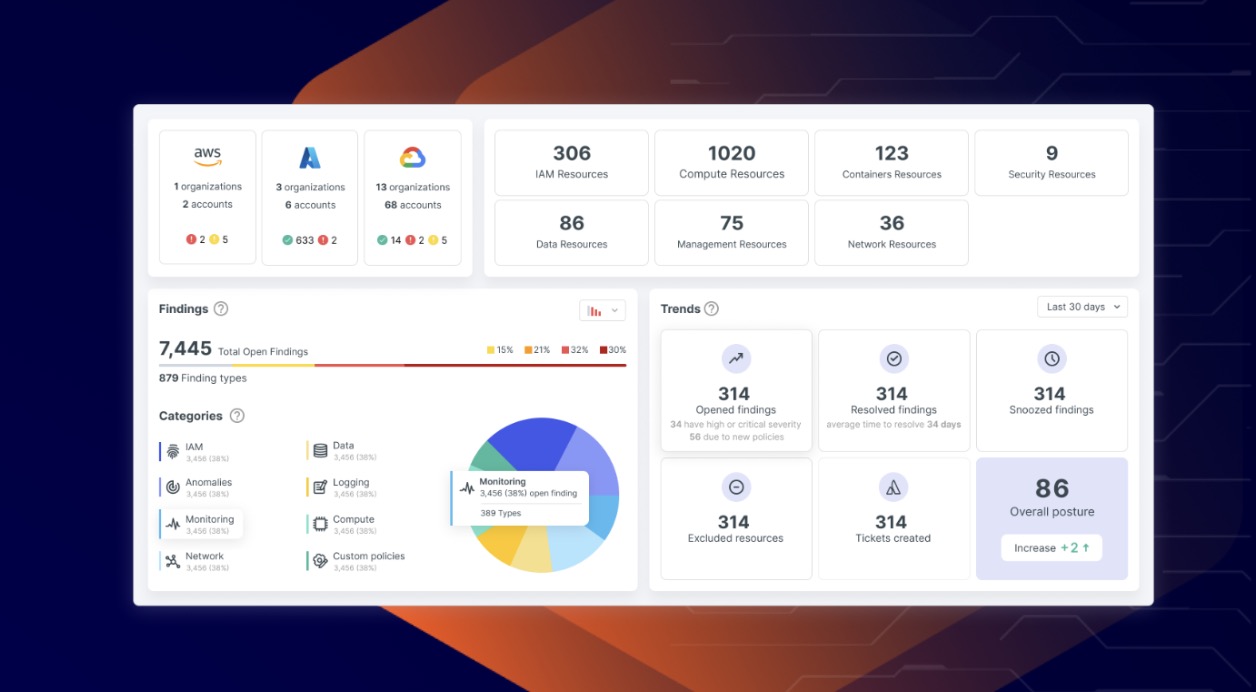
Tenable Cloud Security
Cloud-native security posture management
Tenable Identity Exposure
Secure Active Directory & identity infrastructure
Trusted by Leading Companies





Use Cases & News
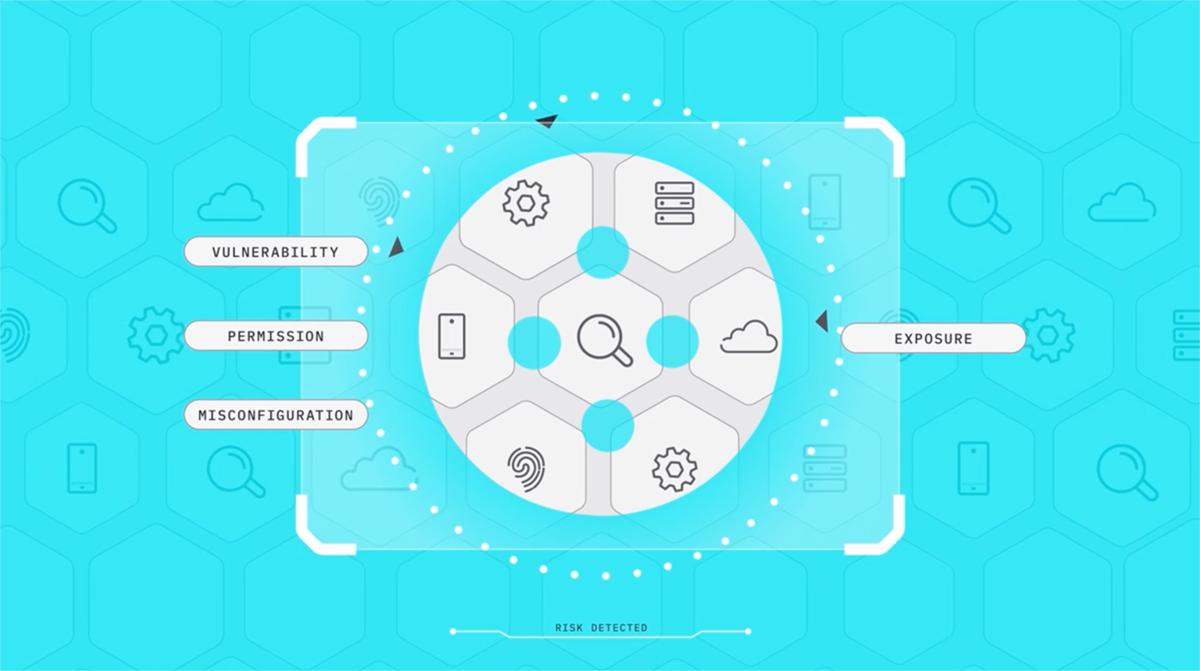
As organizations expand their cloud footprint across multiple providers (AWS, Azure, GCP), maintaining secure configurations and consistent policies becomes increasingly complex. Misconfigured resources, excessive permissions, and compliance drift can expose…
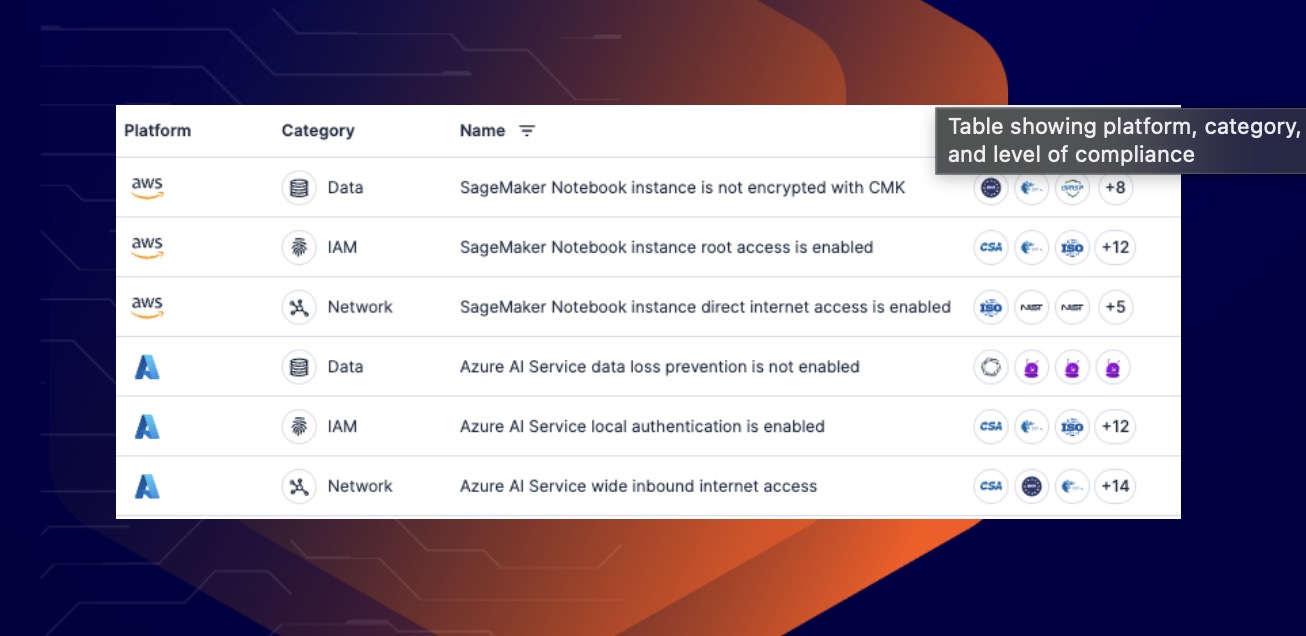
As organizations increasingly adopt AI tools, models, and services, they often lack full visibility into how these AI components interact with cloud environments, user identities, and sensitive data. This creates…
Organizations today must comply with a wide range of internal security policies and external regulatory standards — such as PCI-DSS, ISO 27001, NIST, HIPAA, GDPR and others — while managing…
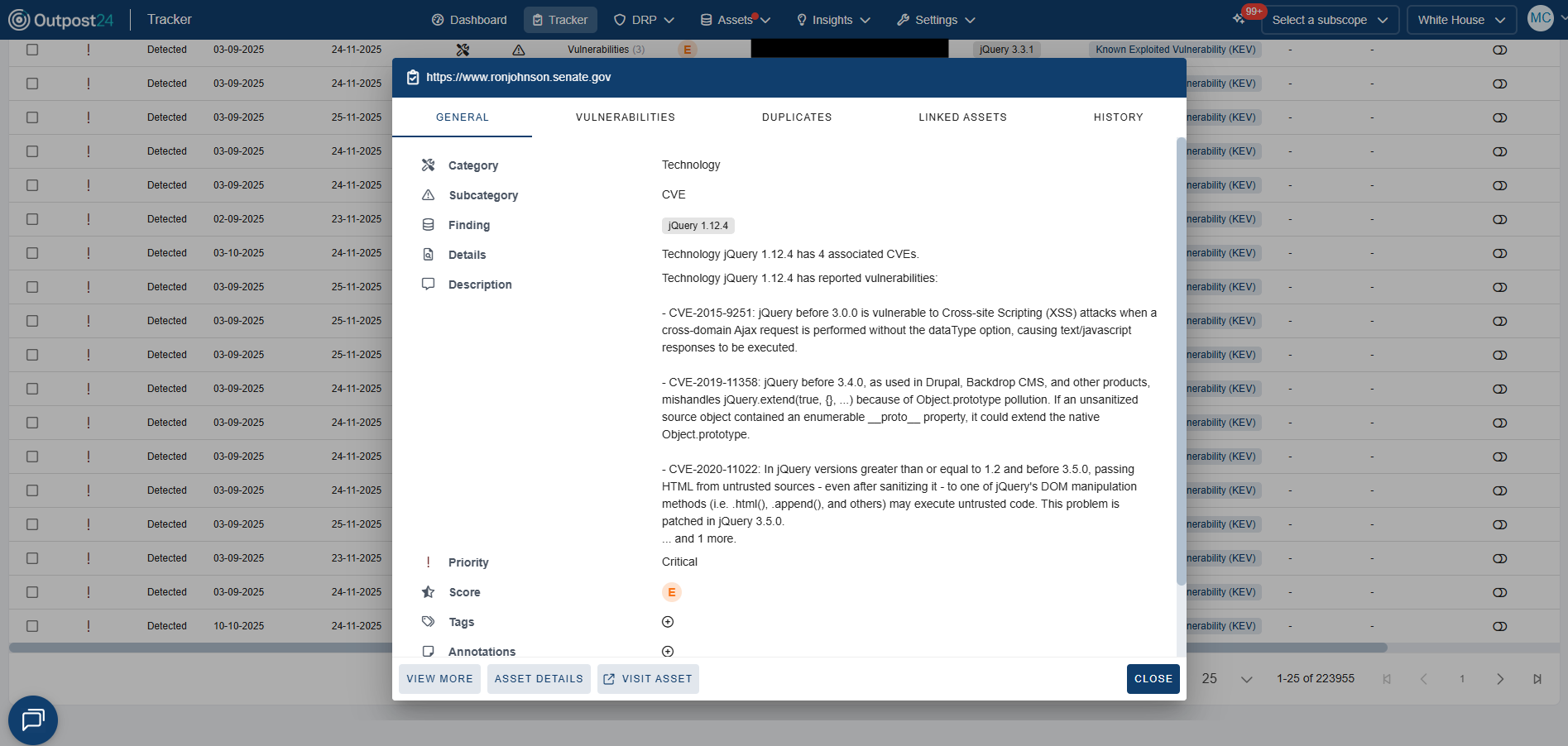
Web applications, mobile apps, and APIs are among the most targeted components in modern IT environments. Attackers constantly probe for weaknesses that could expose sensitive data, disrupt services, or damage…
In a world where digital footprints expand every day, organizations face not just traditional threats inside the network but also evolving dangers lurking outside where attackers look first. Two key…
In today’s digital landscape, your organization’s external attack surface—all the publicly exposed systems, domains, cloud services, APIs and other internet-facing assets—grows faster than most teams can track manually. Every forgotten…