LevelBlue
The World's Leading MSSP — Protecting What Truly Matters
A Word from the CyberLion
Main Features
Most Awarded by Industry Analyst Firms
LevelBlue has been consistently recognized with industry awards since 2005.
Partnerships with All Industry Leaders
Palo Alto, SentinelOne, Check Point, Fortinet, Cybereason, and more.
Proprietary Threat Intelligence
Stay one step ahead of adversaries with a global team of over 1,000 consultants, threat hunters, forensic analysts, and more.
Future-Prof
As threats continue to evolve and expand, LevelBlue remains at the forefront of innovation.
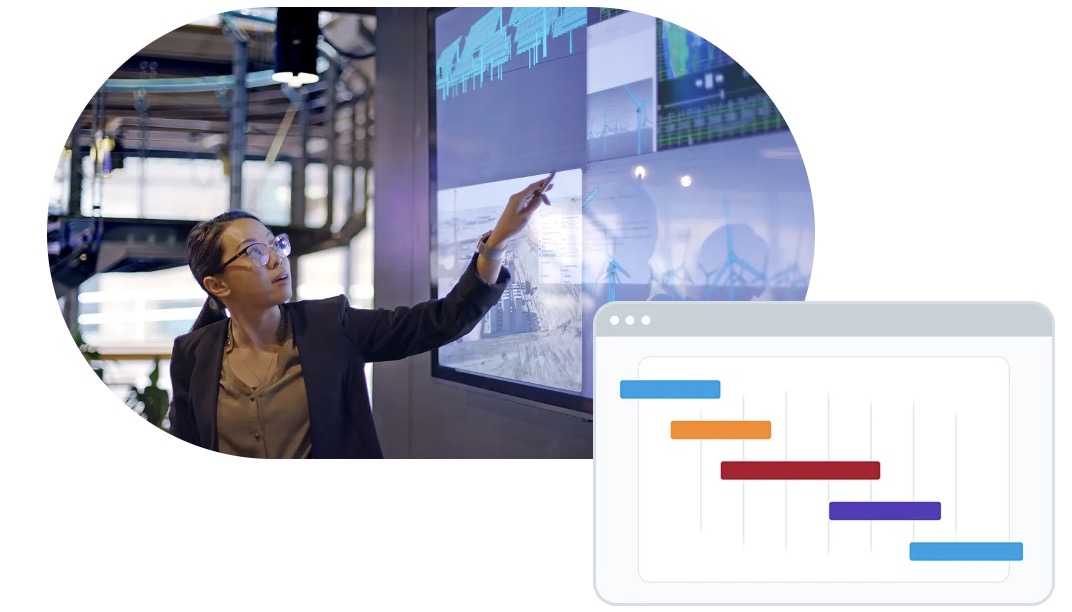
Full-Stack Hybrid Environment Protection
Delivering outcomes with support for 30 telemetry sources and deep expertise in cybersecurity technology optimization
Product Suite
Threat Detection, Investigation & Response (TDIR)
A comprehensive cybersecurity services solution that integrates AI-driven accuracy with expert human insight.
Managed Cloud Security
An expert-led service for protecting public, private, and hybrid cloud environments.
Managed Network Security
An efficient, high-performance solution for securing organizational network access, data protection, and performance optimization.
Trusted by Leading Companies

Use Cases & News
Bridging Autonomous Detection with Real-World Response The partnership integrates SentinelOne’s AI SIEM and AI-driven analytics technology with LevelBlue’s Indigo security platform, which orchestrates security operations across environments alongside its threat…
The Challenge: Organizations today operate in an environment where sensitive data is dispersed across systems, cloud platforms, applications, and third-party vendors — with no full visibility or accurate data mapping….
The Challenge: Modern manufacturing facilities converge IT systems, OT systems, cloud infrastructure, industrial machinery, and legacy environments — a combination that dramatically expands the attack surface. Any breach can result…